The MySQL InnoDB storage engine automatically crashes when it detects corruption in InnoDB tables. In such a situation, you can…
You know that tiny heart attack you get when you see a “suspicious login attempt” notification? That’s your brain catching…
Ever Googled yourself? The results can be terrifying. While you’re worrying about who saw your awkward beach photos, data brokers…
Ever felt that little flutter of panic when you can’t find your phone? Now imagine that feeling when someone has…
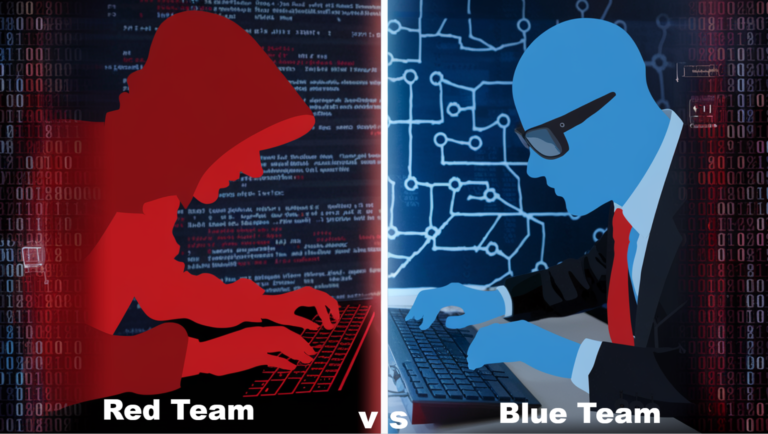
Ever wondered what keeps cybersecurity professionals up at night? It’s not the caffeine—it’s knowing that hackers exploit the same red…
You wake up, reach for your phone, and log in to Instagram—but something’s wrong. Your password is no longer valid, your…
Concerned about online safety yourself? In the digital age, in which we are currently living, cybercrime is waiting around every…
Red teams are vital in identifying vulnerabilities and strengthening an organization’s defenses in the high-stakes world of cybersecurity. But what differentiates…